Industrial cyber threats are rising. Secure-by-design equipment and proactive risk management are among the keys to resilience.
By Patrik Tikka , Product Market Manager, ABB
Mention the phrase “safety hazard” in a manufacturing context, and attention naturally turns to the physical risks that come with industrial life: large-scale fires, explosions, equipment failures. But behind the high‑visibility jackets and hard hats, there’s a quieter risk lurking, one that often strikes without warning: the cyberattack.
Manufacturing has seen the sharpest rise in data breach costs of any industry, with median year-on-year costs climbing by $830,000. And that’s before factoring in downtime, one of the most expensive consequences of a cyber incident. According to a global ABB survey, unplanned outages can cost nearly $125,000 for every hour they persist. It’s proof that the ability to bounce back from cyberattacks must be a cornerstone of any cyber resilience plan.
The convergence of information technology (IT) and operational technology (OT) has expanded the industrial attack surface, from business systems to the factory floor. Staying ahead of both intentional and unintentional threats means getting a good grip on the risks, putting appropriate defences in place, and maintaining them with routine testing and reviews.
Modern manufacturing facilities are intricately connected ecosystems. Attackers no longer have to breach the system, they simply need to find the weakest link. One missed patch, one forgotten device, or one guessable password could function as a potential point of entry to a machine or to a larger network.
A few good options to enhance the security robustness of a system include a thorough inventory of your attack surface and a clear-eyed assessment of vulnerabilities. Every networked component, regardless of how mundane it might seem, could represent a potential access point that warrants case-by-case attention.
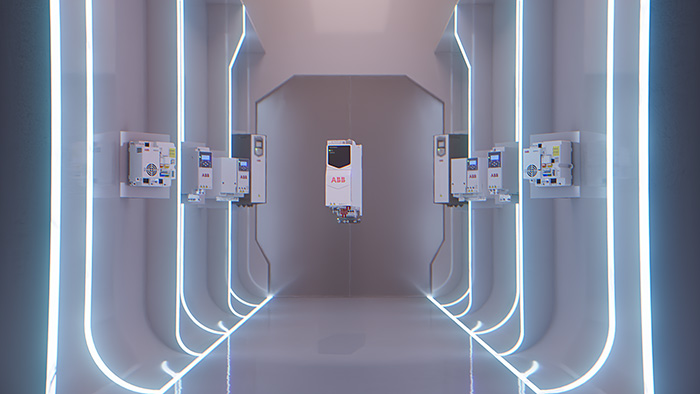
Variable speed drives (VSDs) are a useful case study among other critical components – such as PLCs and HMIs – that could disrupt production if compromised. Their function – adjusting motor speed to match actual demand – sounds straightforward enough, but they’re constantly passing information between individual machines and wider plant networks. If a malicious actor gains control of a VSD, the chances of a disruption go up. Production might grind to a halt or other machinery could be harmed.
Making drives secure-by-design – building protection into them from the start – turns them into front‑line defenders when installed, used and maintained correctly. A secure-by-design approach for VSDs makes practical sense: it simplifies procurement, installation, and usage while enhancing the integrity of the machine or system as a whole when utilized correctly.
With such a mindset, cybersecurity advances at every stage of a product’s life, from development through deployment and beyond. This means that operators could avoid both the cost and the chaos of reactive fixes applied under pressure. But this logic shouldn’t stop at drives. The real goal is to apply the same principles to any device that delivers meaningful value at the system or site level – though only when it is pragmatic to do so or when safety demands it.
A persistent myth in industrial cybersecurity is that, with enough tools and policies, you can completely defend systems from cyber attacks. However, in practice, some residual risk will always be there. So the question shouldn’t be ‘Is there risk of a breach?’, but ‘How much risk are we willing to take, given the cost of mitigation?’.
Investing in security upgrades for production equipment may impact the balance sheet in the short-term, but a successful cyber attack could stop operations entirely, generating losses that might dwarf these expenses.
The trick is to find a pragmatic balance between the residual risk you can tolerate and what you’re willing to spend on protection. That said, this risk-based approach must account for the fact that cybersecurity in industrial settings can directly impact worker safety. When personal safety is at stake, cost is not the most important measure. Safeguards should be deployed where they genuinely add value – prioritizing safety-critical systems – and only after you understand the risks they’re intended to manage, rather than chasing the latest security gadget.
Ultimately, cybersecurity is as much a strategic discipline as a technical one. Choices about which controls to implement, and how widely to roll them out, should be guided by risk assessments and proper cost‑benefit analysis, not by fear or guesswork.
Technology solves only part of the security equation. Many breaches start with a cunning phishing email, a convincing phone call, or a moment of misplaced trust. A single click or impulsive decision could be enough to compromise defenses.
Building a culture of vigilance and healthy scepticism is just as important as deploying firewalls and secure-by-design equipment. Regular training and realistic phishing simulations are a good examples of baseline practice for everyone from operators on the plant floor to senior leadership.
Crucially, cybersecurity cannot live in a small corner of the IT department. It needs to be woven into the whole organization and reinforced by habit and routine. Like a fire drill, regular practice makes sure that when a real threat emerges, people know what to do and how to keep calm under pressure.
Cyber resilience in industrial operations is never complete. The landscape is fluid. Breach techniques evolve, new tools such as AI change the threat profile, and regulators steadily raise the bar.
Rising to this challenge calls for a proactive approach. That means embedding security at the device level, conducting thorough risk assessments, matching level of protection with the cost of an attack, and fostering a culture of continuous vigilance against a threat that will never entirely vanish.
VSDs may be a sensible place to begin, but they’re only the first step. Genuine resilience means knowing the risks your systems encounter and tackling them in ways that are proportionate and regularly revisited. Because in the end, cyber resilience isn’t about perfection – it’s about continuous improvement and readiness.
For more information on ABB’s secure-by-design drives https://www.abb.com/global/en/areas/motion/drives

About the author
Patrik Tikka is Product Market Manager at ABB, where he leads strategy and development for connected, secure drive systems. He is an expert in device-level cybersecurity, functional safety and digital solutions for connected industrial equipment. He has a background in technical sales, business development, and R&D, all with a focus on digital connectivity and security.
Read more from the author:
Comment: Every device matters in industrial cybersecurity | The Engineer, 20th October 2025:
As manufacturers offer more customization than ever before, managing product complexity has become a critical challenge. Tune in with Dan Joe Barry, Vice President of Product Marketing at Configit, who explores how companies are tackling the growing number of product configurations across engineering, sales, manufacturing, and service. He explains how Configuration Lifecycle Management (CLM) helps organizations maintain a single source of truth for configuration data. The result: fewer errors, faster quoting, and the ability to deliver customized products at scale.