Inaction could lock businesses out of key contracts.
By Michael Flavin, SaalexIT
Private contractors doing business with the U.S. Department of Defense (DoD) recently found themselves caught like proverbial “deer in the headlights” as new government guidelines threaten to limit their access to lucrative government contracts. The warning horn has been sounding for some time, but few businesses appear ready for what is heading their way.
Responding to growing concerns over security and cyber threats, the DoD has increasingly focused its attention on cybersecurity. According to Katie Arrington, Special Assistant to the Assistant Secretary of Defense for Acquisition, the U.S. has been losing $600 billion annually in exfiltration, data rights and R&D loss. In 2019, the DoD announced implementation of Cybersecurity Maturity Model Certification (CMMC), ranking contractors’ cyber hygiene on a scale from 1 (“Basic”) to 5 (“State-of-the-Art”).
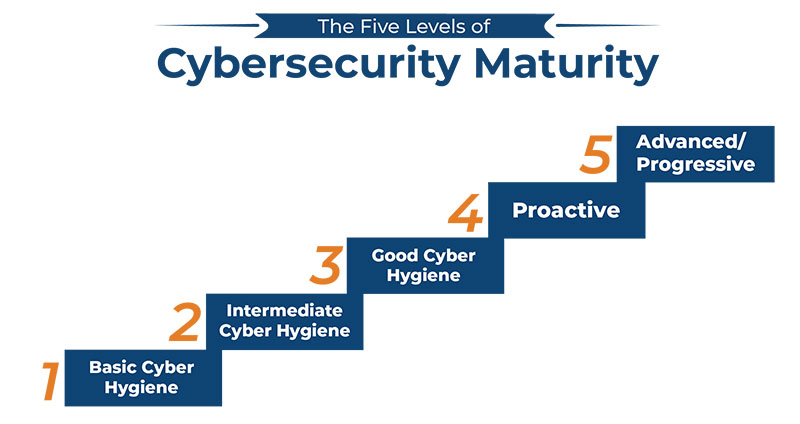
The Cybersecurity Maturity Model Certification (CMMC) program, created and managed by the DoD, ranks contractors on their cyber hygiene.
After soliciting feedback from the industry, the DoD began certifying auditors in January of this year. New requirements for RFIs (Request for Information) will begin June 2020 and certification to bid on RFPs (Request for Proposals) is set for September.
As of this year, cost plus contracts will include a cybersecurity element along with previous components like cost, schedule and performance. In an effort to protect controlled unclassified information (CUI) stored, transmitted or processed on non-federal computer systems, the DoD now requires that contracting be accredited based on NIST 800-171 cybersecurity standards.
NIST 800-171 compliance requires firms to audit networks and systems while addressing appropriate security policies. Companies that cannot prove they have security protections in place and that they are in compliance not only risk missing contract awards, but also the ability to compete for future awards.
By making compliance part of the bidding process, contractors now have to submit to an audit and be able to write to their NIST 800-171 compliance to demonstrate how they will secure their information using measures outlined in the CMMC. Those unable to measure up will be blocked from doing business with an array of federal clients, including the DoD, NASA and the various branches of the military, among others.
How serious is the industry’s current state of cyber readiness? At recent industry event in California, I spoke with a representative from a major defense contractor that provides sensitive technology for military vehicles. He didn’t have encryption on his laptop because, in his own words, “The office IT guy said I didn’t need it.” That should provide some picture of how far the industry has to go meet these standards.
Despite all these regulations bearing down, many companies doing business with the U.S. government appear frozen in place. CMMC implementation is being managed by Arrington’s office, which reports that as of January only about one percent out of the more than 300,000 DoD contractors are currently compliant under CMMC.
“CMMC is going to be law of the land,” said Corbin Evans, the director of regulatory policy for the National Defense Industrial Association. “Yet folks are a little hesitant to make any major moves.”
While some contractors take a wait and see approach to compliance, the government has tried to assuage their concerns with promises to help offset the financial impact of implementing new cybersecurity protections. Arrington is hoping this will soften the blow for companies feeling the pinch from meeting the new standards and encourage more firms to begin moving toward CMMC compliance. Deadlines for auditing and enforcement are quickly approaching. The time for action is now, otherwise these companies risk finding themselves shut out of federal contracts altogether.
For larger enterprises, looking to your own level of compliance may not be sufficient. Many upper-echelon defense and airspace contractors subcontract to small manufacturers for items like replacement parts. In these instances, there is a flow-down effect wherein subcontractors are held to the same standards as primes. Not only will the Boeings and Northrop Grummans to have to show compliance, but also the smaller entities making landing gear assemblies and all the other widgets down the supply chain.
The major aspects of CMMC have already gone into effect. Affected firms will need to avoid the approaching headlights and take steps towards compliance if they want to compete in the federal sector. Rather than remaining in place, smart enterprises are seeking cover in the form of IT consultants with a strong background in NIST 800-171 compliance to guide them in adopting the necessary cybersecurity best practices.

Michael Flavin
About the Author
Michael Flavin, Director of IT Sales at SaalexIT, is an accomplished senior product marketing and sales professional with 18+ years of experience in SaaS, cloud solutions and managed technology services. He recently earned a CyRP certification and is a Certified HIPAA Privacy Associate.
As manufacturers offer more customization than ever before, managing product complexity has become a critical challenge. Tune in with Dan Joe Barry, Vice President of Product Marketing at Configit, who explores how companies are tackling the growing number of product configurations across engineering, sales, manufacturing, and service. He explains how Configuration Lifecycle Management (CLM) helps organizations maintain a single source of truth for configuration data. The result: fewer errors, faster quoting, and the ability to deliver customized products at scale.