Preparing your business to succeed in the “new normal” means mitigating risk in a world of grayzone threat actors.
By Mark Sangster, VP & Industry Security Strategist, eSentire
Modern manufacturing faces a seemingly endless slew of threats. And just when you thought things couldn’t get any more complicated, along comes COVID-19. Whereas the pandemic has brought with it exciting new opportunities for remote work and increased connectivity, these opportunities also came with their own set of problems.
Shortages in off-shored medical equipment over the last few months under the thumb of a pandemic demonstrated the strategic value and critical role that manufacturing plays in the economy and security of the country. Because of manufacturing’s critical role it’s not surprising that it is the target of ne’er do wells, the kind of which aren’t averse to kicking someone when they’re down. Industries across the globe have struggled in recent months to maintain operations while simultaneously coping with unprecedented cyber security challenges that impact the small and medium supply chain and its ability to keep pace with an evolving threat landscape.
While cyber risk isn’t something that can be completely staved off, in order to mitigate its effectiveness, it’s critical that we recognize those external factors that make manufacturers vulnerable to new threats, while also giving careful consideration to how to best prepare our businesses for the “new normal.”
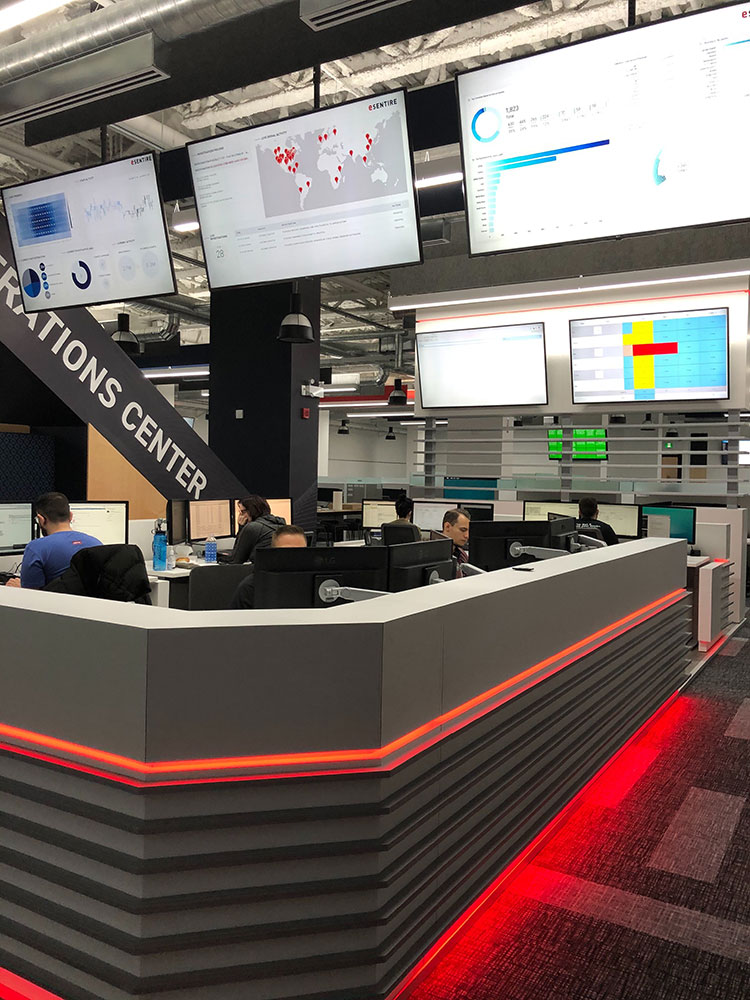
Mitigating cyber risk means security teams must focus not only on detection but response.
In a National Association of Manufacturing (NAM) cyber event held in early June, Jacob Helberg, senior advisor at the Stanford University Cyber Policy Center, stated that while many threat actors are financially motivated, state-sponsored or nation state actors are a different breed, driven instead by political motivation. Specifically, Helberg spoke of “Grayzones” or countries seeking to challenge the United States below the threshold of war.
It’s said that there’s a fine line between love and hate, but it’s a murky world between war and peace. As I describe in my book, No Safe Harbor, for example, the delineation between combatant and non-combatant has evaporated into thin air. There is no such thing as collateral damage anymore. There’s simply damage.
Security operations have seen nation states targeting mid-market firms (read more) and these attacks fall in line with major global events. As a result, organizations feel the aftershocks of tectonic political events such as missile exchanges in the Middle East or trade wars with Asia. Interestingly, these attacks lead to a four-fold increase in annualized cyber insurance claims.
Catherine Lyle, head of claims with Coalition, a leading U.S. cyber insurance and security company, also spoke at the NAM cyber event. Lyle walked us through two specific claims that allowed us to explore the challenges and best practices needed to offset risk through insurance, managing cyber incidents, and making claims.
Her presentation was packed with eye opening metrics:
These are staggering numbers in some respects. Why? For starters, many business leaders thought ransomware was diminishing. Reality, however, is proving just the opposite is true: Ransomware payments are increasing as criminals invest in hands-on-keyboard attacks.
Ransomware as a single-point attack (say, the seizure of a single laptop) is dying, however invested attacks are on the rise. These attacks leverage your own tools against you to metastasize; they plant ransomware across your environment and back-up systems to create massive outages and disruptions. Don’t believe me? Look no further than Travelex at the beginning of 2020, when the London-based currency exchange company had its stores, counters and exchange services shuttered by a New Year’s Eve ransomware attack.
In her talk, Lyle warned organizations against making a payment without first consulting with their general counsel and insurer. In many of the cases she described, the insurer’s agents were able to negotiate with the criminals, reducing ransoms, and in 97.2 percent of the cases, they were able to recover funds lost to fraud.
Cybersecurity is not an IT problem to solve. It’s a business risk to manage. Understanding that global events do affect you, and identifying those that target you and why, are critical to building what Jacob Helberg called, a strategy of “Deterrence by denial” (denying the enemy their objective). It’s an old Cold War theory that stresses the criticality of using tactics to deter the enemy without escalating the threat in order to avoid an all-out war.
Managing cyber risk, including understanding offset strategies such as insurance, is critical to preparing for the worst. Or, in a world of grayzone threat actors who see everyone as fair game, the inevitable.
 About the Author
About the Author
Mark is a cybersecurity evangelist who has spent significant time researching and speaking to peripheral factors influencing the way that legal firms integrate cybersecurity into their day-to-day operations.
Contact:
Agency: Kira Perdue | kira@zagcommunications.com
Author: Mark Sangster | Mark.Sangster@esentire.com
www.esentire.com
As manufacturers offer more customization than ever before, managing product complexity has become a critical challenge. Tune in with Dan Joe Barry, Vice President of Product Marketing at Configit, who explores how companies are tackling the growing number of product configurations across engineering, sales, manufacturing, and service. He explains how Configuration Lifecycle Management (CLM) helps organizations maintain a single source of truth for configuration data. The result: fewer errors, faster quoting, and the ability to deliver customized products at scale.