Job shops must operate against the most updated cybersecurity standards to protect defense contracts critical to their business.
By Scott Sawyer, CTO and co-founder of Paperless Parts
During global disruptions, such as the current COVID-19 pandemic or the recent U.S.-China trade wars, the manufacturing industry plays a crucial part in maintaining the United States’ infrastructure, especially as it relates to the national defense program. Defense and manufacturing companies rely on job shops to produce vital parts and in return, job shops depend on government contracts to drive their businesses forward. But as supply chains continue to become more global, complex and uncertain, job shops need to act now to ensure that their information technology processes and practices are dependable, secure and up-to-date, or risk losing contracts.
Despite having access to extremely sensitive data from their government contracts, such as the specs for a defense article, many job shops do not have updated cybersecurity systems in place to protect this critical information. In fact, many shops are still storing their customer’s drawings and models on shared drives which allow anyone on the network to access any file of their choosing – including hackers looking to mine and steal important information.
Many small job shops are under the impression that, due to their size, they are not the focus for hackers. Contrary to this belief, though, cybercriminals are more likely to hack small job shops because they know that these targets don’t have the same cybersecurity protocols in place as large military vendors. In fact, research shows that the manufacturing industry has one of the highest percentages of exposed sensitive files at 21%.
Hackers use the shops’ networks to find important information related to defense contracts. By using simple tactics like phishing, cybercriminals can spot vulnerabilities on a shop’s network and servers and exploit these to steal data and jump to customer networks. These attacks wreak havoc on any job shop – through monetary losses, a damaged reputation and lack of trust – and consequences can be even more detrimental for those with defense contracts. If, for example, a phishing attack is successful and malware spreads throughout a shop’s email contacts to government employees, their information could be compromised within an hour.
In order to maintain trust with current defense customers and win new contracts, job shops need to take action and implement a robust cybersecurity strategy. To be successful, this strategy must govern how shops securely share customer data and comply with federal compliance procedures.
As more business is conducted digitally, it is critical that job shops have processes in place that inform how to safely transfer data to vendors. Whether it’s a contract, CAD file or even a simple email, shops must be confident that their correspondence is secure. Beyond this, they must be confident that each digital correspondence they receive from a supplier, partner or material distributor is safe, as each unsecured item they receive puts them at risk.
To effectively safeguard customer data, job shops must be proactive about reaching out to vendors to discuss their cybersecurity practices. Cybersecurity guidelines in government contracts don’t just apply to the prime contractor – they also apply to every company in the supply chain. Shops may also consider using secure collaboration tools to ensure they’re safely sharing customer data with third parties. These tools encrypt data while it is being transferred and when it is at rest. Additionally, many will only allow the shared file to be accessed for a certain amount of time, an added layer of security since third parties don’t have indefinite access. Finally, thanks to cloud-based viewing technology, with these solutions users are not required to download and save files, allowing shops to have a better understanding of where their intellectual property lives. Collaboration tools minimize risks for job shops and provide a cost-effective way to strengthen cybersecurity strategies.
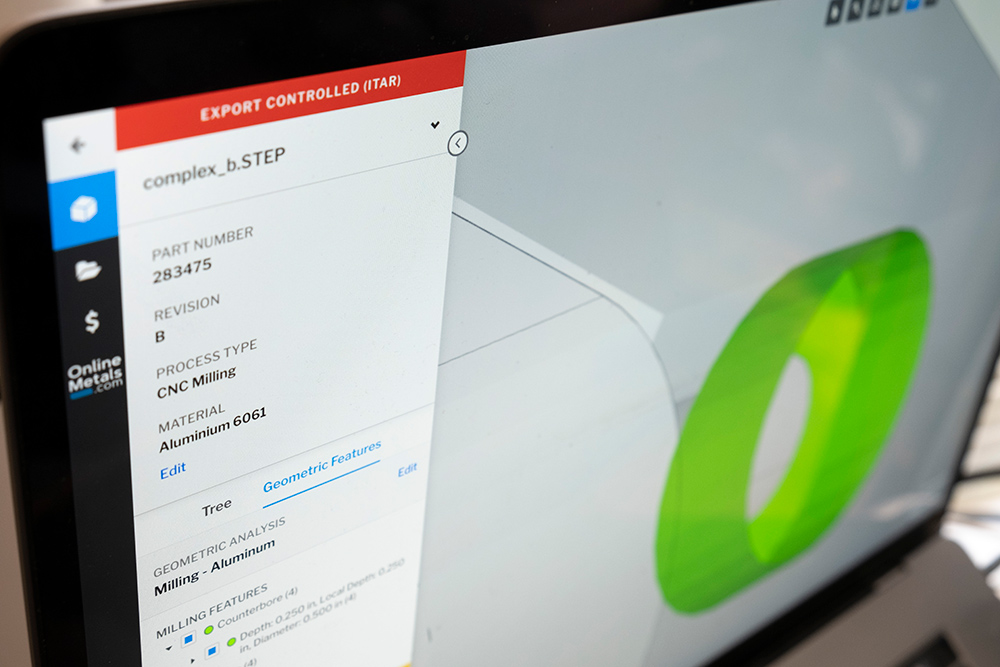
Here, a demonstration part is used to illustrate export control capabilities within Paperless Parts’ Paperless Viewer solution.
Beyond ensuring shared files are secure, organizations must ensure they are compliant with industry standards. Export control laws and the ITAR don’t stipulate how to protect data, but new defense contracts are mandating compliance with new standards like NIST SP800-171. Failing to comply with those industry standards will almost certainly cost job shops business. As cybersecurity continues to be a significant focus for all organizations, these contract provisions will become more robust, likely in the next 6-12 months, with government contractors assessing a job shop’s cybersecurity compliance actively throughout the quote evaluation process and requiring third-party certification.
Because government contractors need to ensure their supply chains are compliant, manufacturers should be prepared to have their supply chains be audited. To ensure that they are following the rules, job shops need to put compliance programs in place. This will involve creating and enforcing internal policies, training employees and investing in tools and technology to securely store and work with sensitive data.
Vulnerability and uncertainty will only continue to rise, especially in today’s climate. As such, job shops need to have a strong cybersecurity strategy in place to continue winning and keeping government contracts. Only by protecting themselves and their customers will job shops be able to flourish and support the U.S. manufacturing and defense industries.

Scott Sawyer
Scott Sawyer is Co-Founder and Chief Technology Officer of Paperless Parts, maker of software solutions for business-minded job shop owners, where he leads an engineering team creating the industry’s most advanced 3D geometric analysis and pricing engine. Prior to founding Paperless Parts, he worked in engineering and leadership roles in consumer electronics and the defense industry. At Lockheed Martin and MIT Lincoln Laboratory, he created technology in the areas of anti-tamper, big data analysis for cybersecurity, and video and radar signal processing, resulting in numerous publications and patents. Scott holds a BSEE from Villanova University and MSEE from the University of Pennsylvania.
Contact: paperlessparts@v2comms.com
As manufacturers offer more customization than ever before, managing product complexity has become a critical challenge. Tune in with Dan Joe Barry, Vice President of Product Marketing at Configit, who explores how companies are tackling the growing number of product configurations across engineering, sales, manufacturing, and service. He explains how Configuration Lifecycle Management (CLM) helps organizations maintain a single source of truth for configuration data. The result: fewer errors, faster quoting, and the ability to deliver customized products at scale.