
February 1, 2019
By Juliette Rizkallah, Chief Marketing Officer, SailPoint
Driven by the requirements of regulatory mandates such as the Sarbanes-Oxley Act (SOX) and the Health Insurance Portability and Accountability Act (HIPAA), identity governance originally emerged as a new category of identity management designed to improve transparency and manageability. By providing organizations better visibility into identities and access privileges, and more effective controls for detecting and preventing inappropriate access, identity governance has become foundational to ensuring compliance and centralized security over organizations’ on-premise and cloud applications, as well as data files.
Manufacturers and their IT leaders are facing increasing amounts of pressure and responsibility when it comes to cybersecurity. For instance, while addressing complex security and compliance challenges brought on by today’s ever-evolving threat environment, they must also enable their end-users to be productive and motivated. At the same time, the long-term digital transformation agendas that almost every competitive organization is going through must also be supported in a secure and seamless fashion. When it comes to this, manufacturing organizations have room to improve.
To help organizations and their IT leaders navigate today’s overwhelming cyber landscape and better understand areas in need of improvement, my company launched an in-depth self-assessment tool that determines Identity Scores. Similar to credit scores, these figures are designed to provide IT leaders a clear roadmap for systematically improving their security and compliance efforts.
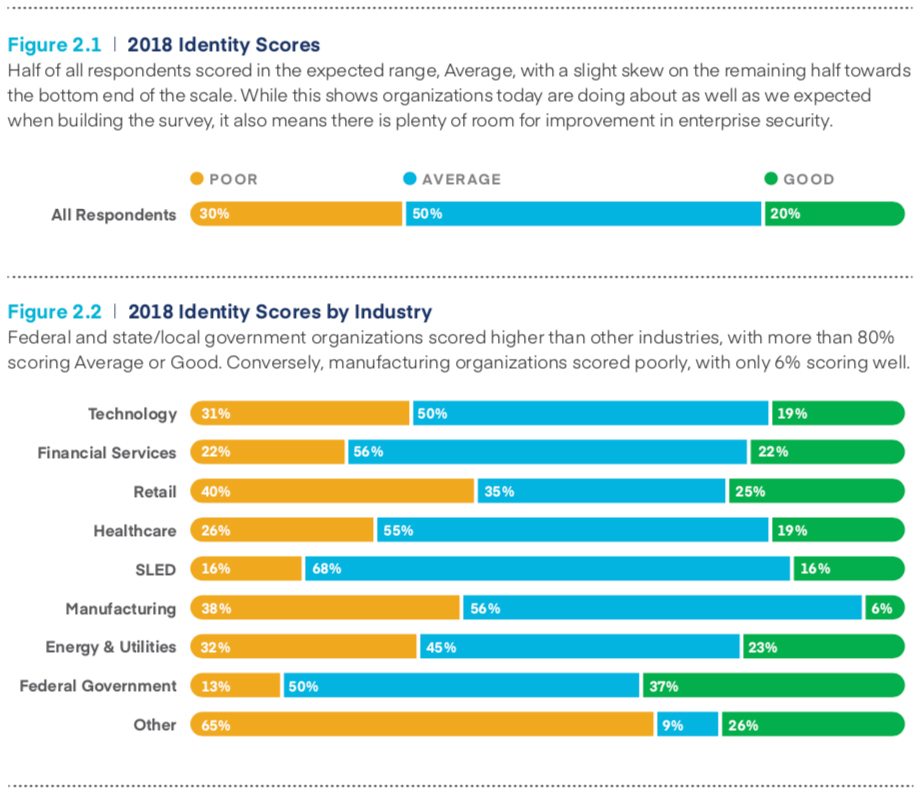
After analyzing 450 Identity Scores across a variety of industries (including manufacturing, alongside technology, retail, healthcare and more), geographic locations and company sizes, we created an Identity Report benchmark and identified three key challenges currently plaguing IT leaders:
Interestingly, out of all the industries surveyed manufacturing organizations have the most room for improvement, scoring only 6 percent ‘good’ and 38 percent ‘poor’ on the Identity Score scale.
Devastating cyber-attacks and debilitating data breaches occur as a direct result of poor cybersecurity practices. The ultimate goal of any identity governance program, then, should be to continuously protect what hackers find most valuable: the identities that hold the keys to critical data, applications and systems. With 1 in 3 organizations leaving their financial data ungoverned, however, more attention must be paid to efficiently delivering secure access to all end-users.
When organizations are able to see, understand and govern their end-users’ access to critical data, applications and systems in real-time, they can proactively protect themselves against potential threats. Furthermore, by incorporating a comprehensive identity program as a strategic component of larger security strategies, organizations can leverage identity governance as a business enabler, using it to properly secure their most valuable assets while also maintaining the competitive pace that today’s market demands.
About Juliette Rizkallah:
A marketing veteran with more than 20 years of experience, Juliette Rizkallah brings a wealth of expertise and pragmatism to SailPoint in her role as Chief Marketing Officer. No stranger to the world of enterprise security, Juliette leads the company’s worldwide marketing efforts, and is responsible for articulating the company vision, product solutions, technology innovations and business purpose to customers, partners and media around the globe.
Juliette has held executive positions and was an agent of growth at some of the world’s largest technology companies, including Oracle, CA, Business Objects-SAP and Check Point Software. She started her career as a strategy consultant at Bain & Company and Arthur Andersen France where she acquired her business impact focus.
Juliette holds an MBA from Harvard Business School and a BA from Ecole Superieure de Commerce de Paris (E.S.C.P.) in Paris, France.
She is also a Forbes Technology Council contributing writer, an invitation-only organization for senior-level technology executives.
If you’re interested in learning more about SailPoint or contacting Juliette Rizkallah, please visit https://www.sailpoint.com/.
As manufacturers offer more customization than ever before, managing product complexity has become a critical challenge. Tune in with Dan Joe Barry, Vice President of Product Marketing at Configit, who explores how companies are tackling the growing number of product configurations across engineering, sales, manufacturing, and service. He explains how Configuration Lifecycle Management (CLM) helps organizations maintain a single source of truth for configuration data. The result: fewer errors, faster quoting, and the ability to deliver customized products at scale.